The hum of satellites overhead, the steady pulse of cell towers, and the faint glow of Wi‑Fi routers all conspire to keep our phones glued to their own digital footprints. In an age where a misplaced device can be found in seconds, it’s no wonder that manufacturers champion GPS as the saviour of navigation and safety. Yet beneath the glossy advertising lies a more unsettling truth: every location ping is a potential data point for anyone with the right tools.
From Lost‑Phone Hero to Data Goldmine
Picture this: you’re hiking in the Swiss Alps, your phone dies at the base of a cliff, and your friend calls you. The “Find my device” feature kicks in, and within moments you know exactly where you are. That same mechanism, however, is a double‑edged sword. Advertisers, law enforcement, and even opportunistic hackers can tap into those coordinates if they possess the right credentials or malicious software.
According to Panda Security’s 2026 guide, modern smartphones constantly record and store location data, a fact that makes them invaluable to anyone who can harvest it. The company warns that “apps, ad companies and even governments” may access this information without the user’s explicit knowledge.
While GPS is indispensable for mapping routes or navigating city streets, its ubiquity also opens doors for covert surveillance. A single data breach could expose a user’s entire travel history—every coffee shop visited, every subway station passed, every hotel checked into over a decade.
The Triad of Tracking Technologies
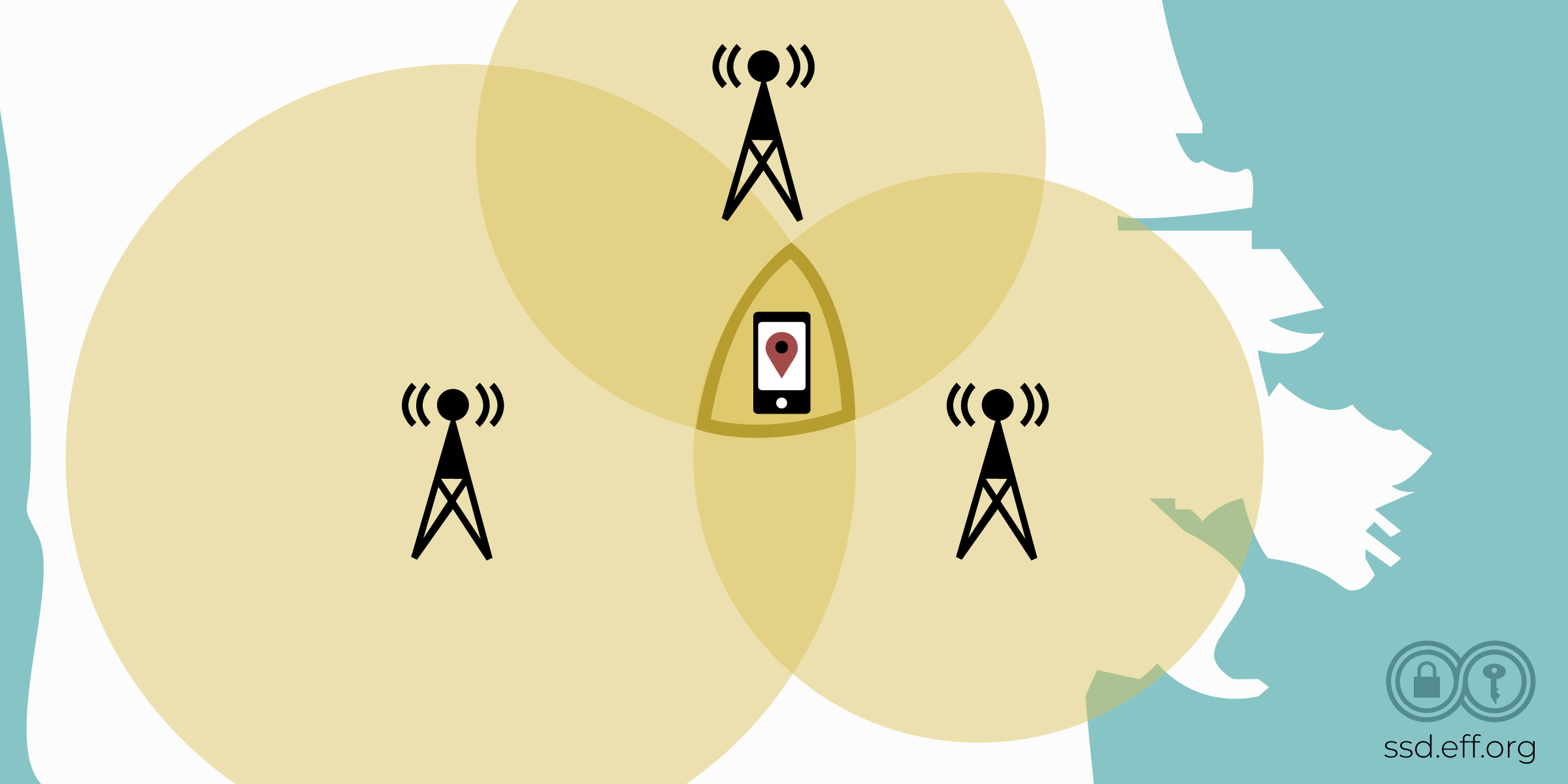
It’s easy to think GPS is the only way phones are tracked, but reality is far more complex. Three primary methods enable location tracking: satellite navigation, cellular triangulation, and Wi‑Fi positioning.
- GPS (Global Positioning System): The satellite constellation provides precise latitude and longitude readings. When you open a map app or a rideshare request, GPS is the first line of defense.
- Cell Tower Triangulation: Even without satellites, your phone communicates with nearby cell towers. By measuring signal strength and time delays, providers can estimate your location within several hundred meters—enough for targeted advertising or basic geofencing.
- Wi‑Fi Positioning: When connected to a router, the phone cross‑references known Wi‑Fi access points on public databases. This method is especially useful indoors where GPS signals are weak.
Each of these methods can be exploited independently or in combination. For instance, a malicious app could disable GPS while still listening to cell tower data, thereby preserving a coarse but actionable location stream.
Why Users Are Still Vulnerable Despite Settings Changes
You might think turning off “Location Services” is the ultimate shield. In practice, it only blocks apps that request fine‑grained coordinates. Background services—such as system updates or carrier network optimisations—continue to ping nearby towers. Moreover, if malware is installed at a deeper level (e.g., a custom ROM or hidden root access), it can bypass user settings altogether.
Even with “Airplane Mode” enabled, some phones still transmit minimal data to the base station for emergency calls. This residual signal can be exploited by sophisticated actors who monitor for any activity from a particular device identifier.
The Legal and Ethical Landscape
Governments often justify location tracking as a public safety measure—think pandemic contact tracing or missing‑person alerts. However, the line between legitimate surveillance and privacy invasion is thin. In 2023, reports emerged that certain U.S. agencies purchased commercial databases of cell phone location records without warrants, raising serious civil liberties concerns.
Meanwhile, corporate giants such as Google and Apple maintain strict internal policies: they do not sell raw GPS data to third parties. Yet the ecosystem of ad tech and data brokers can still harvest aggregated location patterns from anonymised datasets, which are then sold for targeted advertising campaigns.
How Law Enforcement Access Phone Location
The process typically requires a warrant or a court order. Once authorized, law enforcement agencies can request the last known GPS coordinates from a carrier’s database. The phone’s SIM card and unique identifier (IMEI) act as keys to unlock that data vault.
In emergency situations—such as a missing child or a crime scene—a police officer may obtain real‑time location data instantly, bypassing legal hurdles. This power underscores the importance of securing personal devices against unauthorized access.
Practical Steps for the Privacy‑Aware User
Below is a curated list of actions you can take to reduce your phone’s digital footprints without sacrificing everyday convenience:
| Action | Description |
|---|---|
| Restrict App Permissions | Review which apps have “Location” access and disable those that do not need it. |
| Use a Trusted VPN | Encrypt internet traffic to prevent passive eavesdropping on data streams. |
| Install Reputable Anti‑Spyware | Tools like Panda Security can scan for hidden malware that may be siphoning location data. |
| Enable Two‑Factor Authentication (2FA) | Secure your cloud accounts where GPS logs might be stored. |
| Turn Off Background App Refresh | Prevent apps from silently pinging servers even when you’re not actively using them. |
For those who want to take the ultimate step, consider installing a dedicated “privacy mode” app that masks your GPS coordinates or provides fake locations. However, note that many services—like banking apps—detect spoofing and may refuse service.
When to Use Phone‑Number‑Based Tracking
In certain scenarios, you might need to locate a device without the owner’s cooperation—such as a lost child or a stolen vehicle. In such cases, specialized services can retrieve the last known location using only the phone number.
For example, Find mobile by phone number offers a secure portal that aggregates carrier data to pinpoint devices. This tool is invaluable for law enforcement and corporate IT departments looking to recover lost assets swiftly.
The Future: Hybrid Positioning Systems
Industry experts predict that the next wave of mobile navigation will blend GPS with inertial measurement units (IMUs), ultra‑wideband (UWB) signals, and even indoor positioning systems. This hybrid approach promises centimeter‑level accuracy—ideal for autonomous delivery robots or high‑precision logistics.
One such advancement is Real‑Time Kinematic (RTK) correction, which uses reference stations to adjust GPS data in real time. Combined with cellular triangulation, RTK can maintain location fidelity even when satellites are temporarily blocked by buildings or trees.
Implications for Supply Chain Visibility
A recent study from Kings Research (2025) highlighted how GPS‑driven visibility systems have become the backbone of global logistics. By integrating real‑time position data with digital twins and predictive analytics, companies can anticipate delays, reroute shipments, and reduce fuel consumption.
However, this integration also raises new privacy concerns. If a container’s GPS feed leaks to the public, competitors could deduce shipment schedules or supply chain vulnerabilities.
Balancing Convenience and Privacy
The debate over mobile location tracking is far from settled. On one hand, GPS empowers us with navigation, safety alerts, and efficient logistics. On the other, it exposes our movements to a wide array of actors—some benevolent, others malicious.
Ultimately, users must make informed choices: weigh the benefits of real‑time location services against the risks of data exposure; adopt best practices for device security; and stay alert to emerging threats in the ever‑evolving landscape of mobile privacy.